AI & ML in Cybersecurity: Top 5 Use Cases & Examples

AI & ML in Cybersecurity – Top 5 Use Cases & Examples
The world has become digital, and it is proceeding at a fast pace. Digitization means that everything is transforming at high speed. Machine Learning and Artificial Intelligence are the key outcomes of this rapid digitization. These technologies impact every sector and are no exception to the rule of Cyber security.
Cyber-attacks are widespread in nature and affect every business, every individual, even government organizations. Typical cyber-attack means that cyber-criminals or opponents are trying to unauthorized access, modify or damage the targeted computer network/system.
We are living in an era where cybercriminals can achieve their goals at anytime, anywhere in the globe. Now, there is a critical need for Cybersecurity than ever before.
In this article, you will learn various crucial topics like how Artificial Intelligence is playing a significant role in Cybersecurity, what are the use cases of AI in Cybersecurity and examples of AI in Cybersecurity.
ML and AI for Cybersecurity
As cyber-attacks increase in both volume and complexity, conventional ways of detecting malware and threats are failing. Cybercriminals are frequently entering into the digital world with smarter and new and methods to bypass access firewalls and controls and compromise the highly secure networks. One of the only route to prevent these cyber attacks is to be well prepared than cyber attackers or hackers.
AI and ML technology help under-resourced security systems stay ahead of cyber threats. The use of AI in Cybersecurity can aid in broadening the scope of existing Cybersecurity solutions and paving the route for developing new and robust solutions.
By just curating criminal intelligence without using million of research papers, Artificial Intelligence can significantly minimize response times and improve security if a malicious activity or cyber attack is detected.
Also Read:The Revolution of Artificial Intelligence Technology
Get a free quote
Use Cases of AI and ML in Cybersecurity
#1. Network Threat Identification –
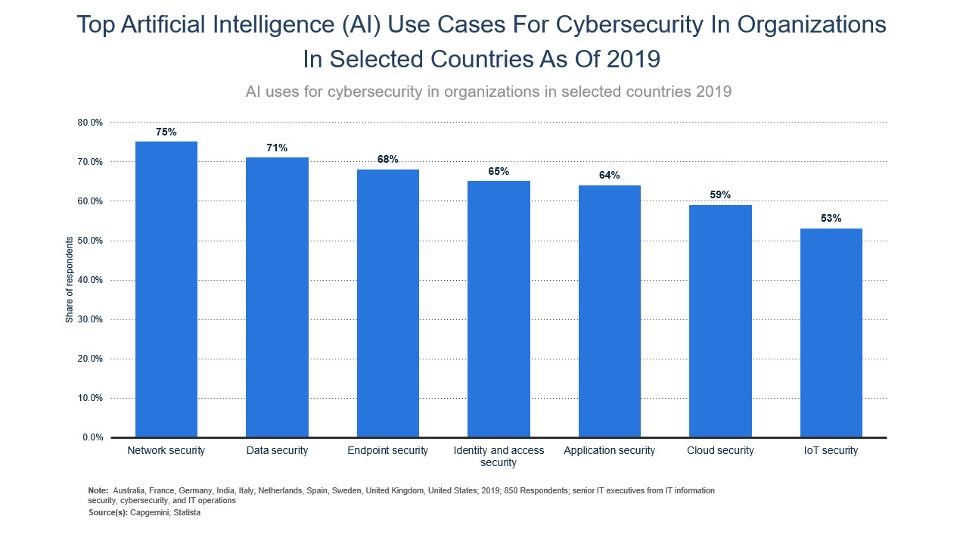
Network security is very important for every organization or business. Understanding the different aspects involved in the network topology is the toughest part of building significant cybersecurity network processes. It will take much time for human cybersecurity professionals to tackle all the information coming in and out of the business network.
Maintaining the networks security of business includes identifying the connection requests that are legitimate and attempting an abnormal connection behavior like receiving and sending large amounts of data or having exceptional programs after the connection to the enterprise network.
The challenging task for Cybersecurity professionals is to determine whether the mobile and web applications or platforms under testing or development are malicious. Large-scale enterprise networks require enormous time to recognize malicious apps in thousands of similar programs, and human experts are not always accurate services.
An AI-powered network security system will monitor all outgoing and incoming calls to detect any suspicious patterns in traffic information. The data in question is generally high for human cybersecurity professionals to accurately classify threats.
Example:
Versive, the AI vendor provides AI-based cybersecurity software which uses dissonant detection to detect vulnerable security threats. The organization says its software helps banks and financial institutions to detect adversary identification and security threats.
Now owned by eSentire, Versive will offer enterprise Cybersecurity named ‘VSE Versive Security Engine’, that helps the financial and banking sector analyze all the transactions and securing related data using ML.
Versive banks refer to the proxy, DNS, and Netflow as inputs to the Versive security engine. This software can monitor networks by using anomaly detection software in order to alert human authorities in case of discrepancies in data similar to events in previous cyber threats.
#2. AI-based Antivirus Software –
Antivirus software can work by scanning files on the company network to check whether any of the file matches the signature of viruses or known malware. The issue with this methodology is that it is reliant on security upgrades for the traditional antivirus software when new viruses are found.
Conversely, AI-powered antivirus software mostly uses anomaly detection to monitor program behavior. Antivirus systems that use AI focus on identifying abnormal behavior generated by programs rather than syncing known malware signatures.
This type of software works well for previously encountered, and recognized threats by its public signature and new threats will be not be detected and resolved easily by this traditional antivirus.
Example:
Cylance, a software company was claimed their smart antivirus product offering AI technology to detect, respond and predict to threats.
Unlike traditional antivirus software, Cylance’s AI-adopted smart antivirus does not require virus signature updates, but over time it will be learning to detect malicious programs from scratch to end.
#3. User Behavior Modeling –
You know? Some kind of security attacks on business systems can motivate particular user in the company by knowing their privacy login credentials without their insight.
Cyberattackers who have taken a client’s accreditations can access to companies network through in fact genuine methods and are very difficult to stop and detect.
Thus, AI-based risk management systems can be utilized to identify changes in those methods and to determine password patterns of explicit customer behavior. In doing as such, they will alert their Cybersecurity teams when the pattern does not work.
Example:
A pioneer AI vendor called ‘Darktrace’ has provided Cybersecurity software, which they utilize as ML to analyse network traffic information in order to understand the baseline behavior of each user and device in the firm.
Taking inputs and other training datasets from subject matter experts, the AI-software learns to detect a vital deviation from normal baseline user behavior and instantly alerts the company to cyber threats.
#4. Fighting AI Threats –
Since hackers are now using AI to detect points entering enterprise networks, organizations should increase the speed at which they can easily detect Cybersecurity. Therefore, the use of AI software to protect against AI-adopted hacking may become an essential part of security defence protocols in the coming years.
In the past few years, firms across the globe have succumbed to ransomware and cyberthreats attacks such as Notepeta and WannaCry. These kinds of cyber attacks will spread fast and affect a large number of computers. Those who carry out this type of attack are more likely to use AI technology in the future. The benefit that Artificial Intelligence can give these hackers is similar to what AI provides in companies: faster scalability.
Example:
Cybersecurity Technology Company, Crowdstrike says that their security software called ‘Falcon Platform’ uses Ai technology to safeguard against ransomware threat and risk. The cyber security software uses anomaly detection for end-point security in their enterprise networks.
#5. Email Monitoring –
Businesses have to understand the importance of monitoring email conversation to avoid Cybersecurity hackings such as phishing. ML-based monitoring software can now help in speeding up the detection of cyber threats and developing detection accuracy.
A wide range of AI technologies is used for monitoring. For example, some software will use email to view email, to see if the email contains any features that indicate threats, like pictures of a specific size.
In other cases, NLP (Natural Language Processing) will be used to read the text through incoming and outgoing emails to identify patterns or phrases in the message associated with phishing efforts. Business can find whether the email recipient, sender, attachment, or body is threatened, by using anomaly detection software.
Example:
A famous software company in London, Tessian offer email monitoring AI software that helps financial institutions to prevent phishing attacks, misdirected emails, and data breaches.
Tessian’s software uses anomaly detection and NLP at various stages to recognize which emails are Cybersecurity threats.
Also Read: 5 Examples of Artificial Intelligence In Business Applications
The Future of AI in Cybersecurity
The use of artificial intelligence in cybersecurity can be named still as new at the moment. Companies make sure that their systems are prepared with the inputs of cybersecurity specialists who improve the software at identifying cyber attacks with more precision.
Organizations need to comprehend that these systems are just as perfect as the data they gave. AI-based systems are commonly called as “garbage, garbage out” systems and need an information-driven way to deal with AI ventures for continued business success.
One challenge for enterprises that use purely AI-based security detection ways is to reduce the false-positive identifiers. This can be easily done because the software knows what is tagged as false positive reports.
Once the baseline of behavior is built, the AI-algorithms can flag statistically important deviations and alert cybersecurity analysts that further investigation is must.
Final Words
Nowadays, cybersecurity applications are one of the trending AI applications. This is in large part because these applications rely on anomaly detection, which is well suited to machine learning (ML) models.
Some of the multi-national companies already have a team of existing cybersecurity professionals, IT infrastructure, and product development budgets to deal with massive data.
Would you like to integrate AI technology to avoid cyber-attacks and improve the overall security position of your business?
Please contact us. We will guide you on the right path!
Get a free quote





